基于openssl的https服务配置
CA服务器:192.168.75.131
httpd服务器:192.168.75.128
操作系统版本:redhat 6.5(x_86_64)
./configure --prefix=/usr/local/apache --enable-so --enable-ssl --enable-cgi --enable-rewrite --with-zlib --with-pcre=/usr/local/pcre --with-apr=/usr/local/apr --with-apr-util=/usr/local/apr-util --enable-mpms-shared=all --with-mpm=event --enable-proxy --enable-proxy-http --enable-proxy-ajp --enable-proxy-balancer --enable-lbmethod-heartbeat --enable-heartbeat --enable-slotmem-shm --enable-slotmem-plain --enable-watchdog --with-ssl=/usr/local/openssl
一、生成自签证书
# yum install openssl -y
# cd /etc/pki/CA/
# (umask 077;openssl genrsa -out private/cakey.pem 2048) #生成私钥
# ll private/
total 4
-rw-------. 1 root root 1679 Feb 18 17:49 cakey.pem
生成自签证书的时候会有很多选项需要填写,如果不想填,可以编辑配置文件,更换默认值
# cd ../tls/
# diff openssl.cnf openssl.cnf.orig
130c130
< countryName_default = CN
---
> countryName_default = XX
135c135
< stateOrProvinceName_default = GuangDong
---
> #stateOrProvinceName_default = Default Province
138c138
< localityName_default = ShenZhen
---
> localityName_default = Default City
141c141
< 0.organizationName_default = SmallFish Company Ltd
---
> 0.organizationName_default = Default Company Ltd
148c148
< organizationalUnitName_default = Tech
---
> #organizationalUnitName_default =
# openssl req -new -x509 -key private/cakey.pem -out cacert.pem -days 3665 #根据私钥给自己生成一个自签证书,这个证书可以给用户使用的
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter ‘.‘, the field will be left blank.
-----
Country Name (2 letter code) [CN]:
State or Province Name (full name) [GuangDong]:
Locality Name (eg, city) [ShenZhen]:
Organization Name (eg, company) [SmallFish Company Ltd]: #给别人签发的公司也必须是这个
Organizational Unit Name (eg, section) [Tech]:
Common Name (eg, your name or your server‘s hostname) []:ca.smallfish.com #发给自己的证书
Email Address []:admin@smallfish.com
# cd /etc/pki/CA/
# touch index.txt
# echo 00 >serial
# tree .
.
├── cacert.pem
├── certs
├── crl
├── index.txt
├── newcerts
├── private
│ └── cakey.pem
└── serial
二、web服务器端,生成证书颁发请求
# cd /usr/local/apache/conf
# mkdir ssl
# cd ssl/
#(umask 077;openssl genrsa 1024 > httpd.key)
Generating RSA private key, 1024 bit long modulus
.......++++++
.............................++++++
e is 65537 (0x10001)
# ll
total 4
-rw-------. 1 root root 887 Feb 8 18:40 httpd.key
# openssl req -new -key httpd.key -out httpd.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter ‘.‘, the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:GuangDong
Locality Name (eg, city) [Default City]:GuangZhou
Organization Name (eg, company) [Default Company Ltd]:SmallFish Company Ltd #必须是CA证书中填写的是同一个公司,不如后面生成公司证书的时候会报错
Organizational Unit Name (eg, section) []:Tech
Common Name (eg, your name or your server‘s hostname) []:www.vip.com
Email Address []:www.vip.com
Please enter the following ‘extra‘ attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
[root@master ssl]#
# scp httpd.csr 192.168.75.131:/tmp
三、CA服务器签发证书
# openssl ca -in /tmp/httpd.csr -out /tmp/httpd.crt -days 3650 #公司名称不一样,报错了
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
The organizationName field needed to be the same in the
CA certificate (SmallFish Company Ltd) and the request (vip Ltd)
# openssl ca -in /tmp/httpd.csr -out /tmp/httpd.crt -days 3650
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 0 (0x0)
Validity
Not Before: Feb 18 10:10:26 2016 GMT
Not After : Feb 15 10:10:26 2026 GMT
Subject:
countryName = CN
stateOrProvinceName = GuangDong
organizationName = SmallFish Company Ltd
organizationalUnitName = Tech
commonName = www.vip.com
emailAddress = www.vip.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
68:4F:A6:95:E8:65:0D:FE:9E:E2:81:31:8A:AF:69:3A:4C:43:E0:94
X509v3 Authority Key Identifier:
keyid:AA:27:66:F1:0F:7A:7C:CA:CD:85:95:1F:D5:92:5A:36:23:FE:1A:36
Certificate is to be certified until Feb 15 10:10:26 2026 GMT (3650 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
[root@slave0 CA]# cat index.txt
V 260215101026Z 00 unknown /C=CN/ST=GuangDong/O=SmallFish Company Ltd/OU=Tech/CN=www.vip.com/emailAddress=www.vip.com
[root@slave0 CA]# cat serial
01
[root@slave0 CA]# tree .
.
├── cacert.pem
├── certs
├── crl
├── index.txt
├── index.txt.attr
├── index.txt.old
├── newcerts
│ └── 00.pem
├── private
│ └── cakey.pem
├── serial
└── serial.old
4 directories, 8 files
# scp /tmp/httpd.crt 192.168.75.128:/usr/local/apache/conf/ssl
vim /usr/local/apache/conf/extra/httpd-ssl.conf
<VirtualHost _default_:443>
DocumentRoot "/usr/local/apache/htdocs"
ServerName www.vip.com:443
ServerAdmin admin@vip.com
ErrorLog "/usr/local/apache/logs/error_log"
TransferLog "/usr/local/apache/logs/access_log"
SSLEngine on
SSLCertificateFile "/usr/local/apache/conf/ssl/httpd.crt"
SSLCertificateKeyFile "/usr/local/apache/conf/ssl/httpd.key"
LoadModule socache_shmcb_module modules/mod_socache_shmcb.so
LoadModule ssl_module modules/mod_ssl.so
LoadModule slotmem_shm_module modules/mod_slotmem_shm.so
Include conf/extra/httpd-ssl.conf
# /usr/local/apache/bin/httpd -t
Syntax OK
# /usr/local/apache/bin/apachectl start
# lsof -i:80
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME
httpd 13445 root 4u IPv6 349321 0t0 TCP *:http (LISTEN)
httpd 13446 daemon 4u IPv6 349321 0t0 TCP *:http (LISTEN)
httpd 13447 daemon 4u IPv6 349321 0t0 TCP *:http (LISTEN)
httpd 13448 daemon 4u IPv6 349321 0t0 TCP *:http (LISTEN)
# lsof -i:443
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME
httpd 13445 root 6u IPv6 349329 0t0 TCP *:https (LISTEN)
httpd 13446 daemon 6u IPv6 349329 0t0 TCP *:https (LISTEN)
httpd 13447 daemon 6u IPv6 349329 0t0 TCP *:https (LISTEN)
httpd 13448 daemon 6u IPv6 349329 0t0 TCP *:https (LISTEN)
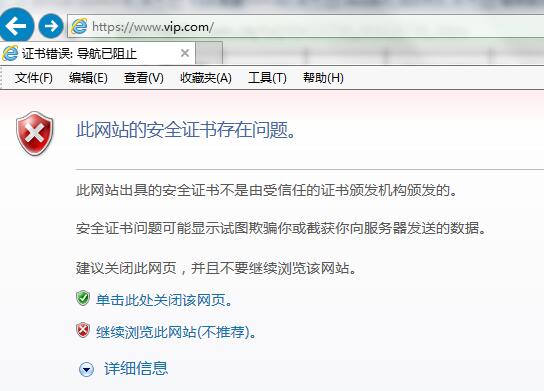
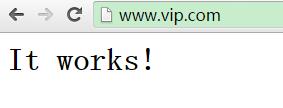
访问:
192.168.85.128 www.vip.com
2、安装证书
本文出自 “小鱼的博客” 博客,转载请与作者联系!
原文:http://395469372.blog.51cto.com/1150982/1743322